https://www.haproxy.com/documentation/aloha/9-5/traffic-management/lb-layer7/http-redirection/ http-request redirect location <loc> [code <code>] [<option>] [<condition>]
acl vhost hdr(Host) www.example.com acl rootRequested path / http-request set-path /the/new/url if vhost rootRequested
https://www.haproxy.com/documentation/aloha/9-5/traffic-management/lb-layer7/http-rewrite/ https://www.haproxy.com/documentation/aloha/9-5/traffic-management/lb-layer7/writing-conditions/
[ALERT] 165/160545 (29257) : http frontend 'myFrontend' (/etc/haproxy/conf.d/myConfig.cfg:6) tries to use incompatible tcp backend 'myBackend' (/etc/haproxy/conf.d/myConfig.cfg:44) as its default backend (see 'mode').
Stuff below is specific to my setup (HTTP + HTTPS frontends + content switching), do NOT apply it as-is !!!
In /etc/haproxy/conf.d/myConfig.cfg, change :frontend myFrontend bind 12.34.56.78:80 mode http default_backend myBackend frontend mySslFrontend bind 12.34.56.78:443 mode tcp default_backend myBackendinto :
frontend myFrontend bind 12.34.56.78:80 mode tcp default_backend myBackend frontend mySslFrontend bind 12.34.56.78:443 mode tcp default_backend myBackend
mars 20 11:06:49
hap01
haproxy[18799]:
12.34.56.78:18593 [20/Mar/2018:11:06:49.794]
qlf-ae_https~
qlf-be-ae/
was02
47/0/3/10/60
500
518
- -
----
97/1/0/0/0 0/0 "GET
/some/resource HTTP/1.1"
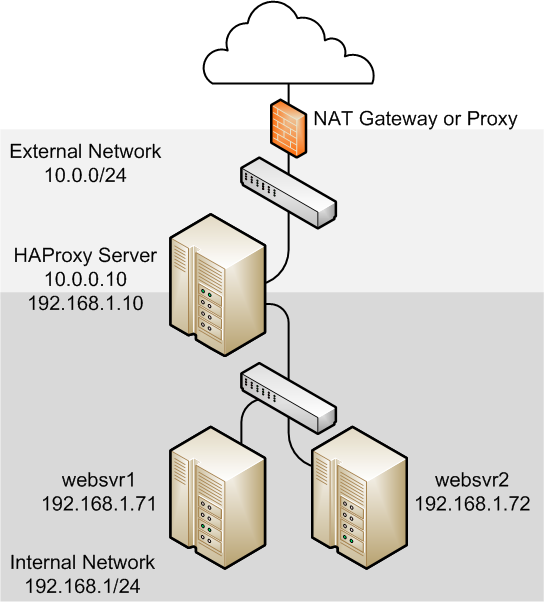
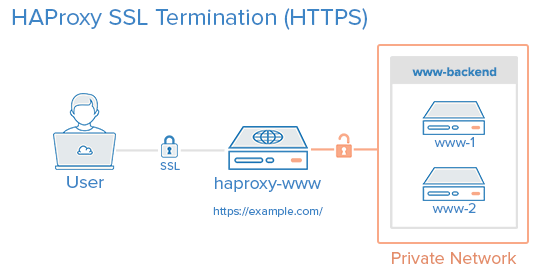
HAproxy is a solution offering high availability, load balancing, and proxying for TCP and HTTP-based applications. It is particularly suited for very high traffic web sites and powers quite a number of the world's most visited ones. Over the years it has become the de-facto standard open-source load balancer, is now shipped with most mainstream Linux distributions, and is often deployed by default in cloud platforms. (source).
HAProxy also has an enterprise edition called HAPEE.
See also Alternate / simpler solutions to HAProxy.
option http-server-close enables HTTP connection-close mode on the server side while keeping the ability to support HTTP keep-alive and pipelining on the client side.